November 29th, 2013

There are a number of precautions you need to take in order to stay safe online. From firewalls to updated antivirus software, there are plenty of tools that can prevent a disastrous cyber attack or data breach. These tools still don’t guarantee your safety, however. Even with precautions in place, it’s important to understand where the majority of threats come from and avoid them altogether with safe surfing techniques. Ron Johnson, of Business2Community, listed some of the most common causes of security breaches and how to avoid them.
Open WiFi networks are found nearly everywhere you go, but they’re far from secure. Any data you send over public WiFi is easily intercepted and stolen by a third party. This doesn’t mean you shouldn’t ever connect to public WiFi. It means you need to be extra careful about what sites you access while using this type of unsecured network. Viewing and reading websites likely won’t cause a problem, but don’t log-in to any online accounts or your password could be compromised.
Most users understand the dangers in giving other people their password, but sometimes even the most savvy users give out their log-in information without even thinking about it. For example, if you’re having difficulty with an account, a customer service representative might ask you for your password. This doesn’t necessarily mean they are going to misuse it, but it’s always a good idea to change passwords once you’ve told them to anyone, including a help desk. They might not always be as careful with your information as you would be. It’s also never a good idea to share accounts with others, even friends or family. If you want to allow another individual to access your account, change the password, give them the new log-in information, then change it again once they’re finished.
Downloading anything should be a decision that every user is cautious of. Even seemingly trusted websites can be compromised and a file you download could end up infecting your system with malware. If you’re prompted to download an application, like a media player, go to that player’s official website to download. Be sure to scan every file downloaded with your antivirus program before opening. As for email attachments, don’t download them unless you were expecting a file to be sent to you and you know exactly what it is.
Speaking of email, phishing scams are a popular method for stealing your information and hacking into your online accounts. These scams have grown more sophisticated. Often, an email will appear to be from a legitimate website where you hold an account. It will claim there’s been a problem and you need to log-in immediately, or download software, or even put in credit card information. If you have any questions about the legitimacy of these emails, contact the website or business directly, by phone if possible. There’s never a time when a business will email and need your credit card information.
By learning some of these common hacker tactics, you’ll be able to be smarter about your online habits and avoid potential threats.
If you’d like to improve security at your home or business to further safeguard from malware, phishing scams, hacking and more, contact Geek Rescue at 918-369-4335.
November 27th, 2013

A new piece of malware, a trojan called ‘Neverquest’, has security experts scrambling and forecasting a number of future attacks. As Lucian Constantin of Computer World reports, Neverquest has the ability to spread quickly and steal your financial information.
It’s believed that the Neverquest trojan originated in July, but the first attacks didn’t occur until months later. Now, experts have spotted thousands of uses of Neverquest and they expect to see that number spiral out of control soon.
In many ways, Neverquest is similar to other malware that targets financial websites. It’s able to insert its own forms into websites opened in Internet Explorer and Mozilla Firefox. It steals log-in information entered into these malicious forms and can also control your computer remotely.
Those are scary features, but that’s not all Neverquest can do. The trojan comes with 28 websites where criminals will be able to steal log-ins that control finances. These are the most popular banking sites and online payment services. To expand the number of sites it’s used with, and to ensure that every infected user is at risk, the trojan also monitors a victim’s activity and searches sites visited for keywords like ‘account summary’ or ‘balance’. When it discovers those sites, it alerts it’s host so they can begin attacking those sites as well.
In order to gain access to your computer, hackers first infect websites. When you visit one of these infected websites, vulnerabilities in browser plug-ins are used to install malware directly onto your hard drive. Spam email and links sent over social media are also used to infect users.
To keep your computer, and bank account information safe, don’t follow suspicious looking links and don’t visit untrusted websites. Keep your antivirus program running and up to date, as well.
If you have malware, trojans or viruses on your computer, bring it to Geek Rescue or call us at 918-369-4335. We clean infected machines and help you protect against future attacks.
November 27th, 2013

There are a number of reasons to focus more on security for your mobile device, or the mobile device of your employees. For personal use, 7-percent of smartphone owners have been the victim of identity fraud, which is a substantially higher rate than the rest of the population. For businesses, about two-thirds use the bring your own device model, but only about 4-percent manage the company data their employees access with personal devices. In both of these examples, the issues stem from a lack of mobile security. Eyal Manor, of Information Week, writes that companies must focus on the data being accessed by employees, rather than the devices themselves, to improve security.
Many smartphone users don’t keep their apps and operating system updated, which opens security holes. Many don’t use a passcode either. There’s more and more mobile specific malware being introduced every day. These would be reasons to institute mobile device management, but when employees are using their personal devices, it’s difficult for more businesses to demand that type of access and control. Instead, here are three ways to improve security by focusing on the data being accessed, rather the individual device.
This tactic takes all of business-centric data stored on an employees device and locks it down in a special, encrypted area. Rather than putting controls on the entire device, companies are able to control only the encrypted area allowing them to ensure the safety of company data.
Users may not have strict security in place to restrict who can access their device, but for company information enhanced authorization can be installed so that data isn’t compromised in the case of theft or a lost device. Similar to containerization, only vital company data would be stored behind additional walls, which would require an employees log-in information to get through.
Regardless of the other safety measures taken to protect data, if it’s not encrypted, it isn’t safe. Hackers are continually evolving their tactics to get past enhanced security, so data theft remains a possibility. If your data is encrypted, however, you take added precautions that stolen data can’t be accessed by a third party, and won’t come back to damage your company. Remember that encryption is important both for stored data, and for data being sent between two parties.
For help improving the security of your company’s data, call Geek Rescue at 918-369-4335.
November 26th, 2013
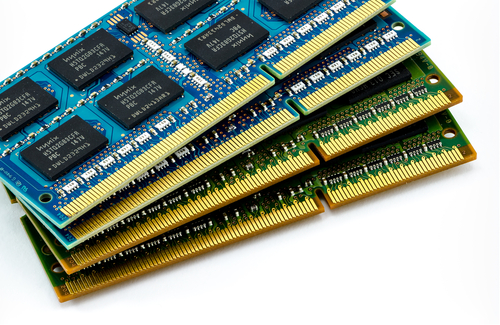
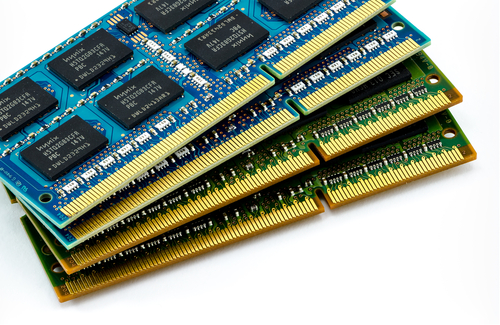
Adding more RAM to your computer has long been considered a sure-fire way to improve performance. But, as this video by TechQuickie points out, that’s not always true anymore.
The addition of RAM can make a computer faster in some situations, but not always. If you are using your computer for basic tasks, such as email, normal web browsing and Microsoft Office, there’s likely no benefit from adding more RAM, even if you’ve noticed your system is running slow. PCs that are less than three years old usually come with more than enough RAM for the average user. If your computer is older than three years, it’s possible that adding RAM would help performance, but it’s also likely that there are other issues causing your system to slow down.
In many cases, it’s not a lack of RAM causing the decrease in performance. Instead, it’s likely a virus or malware, or a damaged or malfunctioning component. Before buying more RAM for your PC, it’s worth it to check your entire system and try to pinpoint exactly what needs to be fixed or improved.
Part of that diagnostic check can be done through Task Manager for Windows users. Task Manager is home to a Performance Monitor, which will show you a graph of your RAM usage. If you notice that most of your RAM is being used, check the running processes to find out what applications are hogging your resources. In many cases, a slight alteration of your habits with applications, or finding alternatives to bloated applications, can eliminate the need for more RAM and improve performance.
If you check the Performance Monitor and notice that RAM isn’t being used excessively, but your system is running slowly, that’s a tell-tale sign that there’s other issues at work. In some cases, this is a suggestion that it’s time to upgrade to an entirely new PC.
Before you throw money away on computer improvements that might not actually help performance, be sure to perform a diagnostic test to pinpoint the actual problem. Bring your computer, or other device, to Geek Rescue. We diagnose what’s causing your system slow down and fix it quickly. Call us at 918-369-4335.
November 22nd, 2013

Malware for both PCs and smartphones continues to be a growing problem worldwide. Adam Greenberg, of SC Magazine, reports that much of the new malware discovered in the past quarter uses techniques to falsely verify, or by-pass altogether, digital signatures used to validate legitimate applications and files.
Researchers with security company McAfee reported a 30-percent increase in malware for Android,m which equates to about 700-thousand new pieces of malware. Most of this mobile malware is known as “Exploit/MasterKey.A”, which allows for the avoidance of digital signature validation.
This method is also being used in the increasing threat of malware for PCs. Malware for PC users using falsified digital signatures is up 50-percent this quarter with more than 1.5-million new pieces identified.
These latest tactics are more intelligent ways of making users believe a file of application they’ve downloaded is safe for use. Antivirus software company, BitDefender, reported one malware scam that convinces users that they’re downloading an antivirus program called ‘Antivirus Security Pro’. It contains a stolen digital signature and when run, it identifies false examples of malware and demands money to fix the problem.
Examples like this are why it’s important for users to keep security software up to date. Antivirus applications struggle to keep up with the latest tricks of cyber criminals, and it’s impossible for them to catch the latest pieces of malware that attempt to infect your system if they’re out of date.
If your computer or smartphone falls victim to malware, or you’d like to improve your security before the next attack happens, call Geek Rescue at 918-369-4335.
November 21st, 2013

Spam emails began as a nuisance, but one that ultimately wouldn’t harm your computer. Since those early days, spam has evolved to be much more malicious. Now, spam often is the first step to infecting your machine with malware, trojans, keyloggers and viruses. Spam can be used to steal your identity and hold your computer for ransom. Jeff Orloff of The Email Admin posted some threats to be on the look-out for and some tips for how to stay safe.
Cryptolocker is the latest threat making headlines. The trojan is a form of ransomware that first surfaced in August. Most commonly, it stems from an email attachment that infects the victims computer when it’s downloaded. The cryptolocker is then able to encrypt certain types of files on your system and holds them for ransom. To decrypt the data, a payment is required. Often, there is a deadline that goes along with this demand for money. While some users report they’ve paid the ransom and their files were encrypted, others have paid and seen no results. Unfortunately, even professionals struggle to decrypt files that have fallen victim to a cryptolocker.
In less than a week, more than 12-thousand users reported being infected by a cryptolocker in the US. This isn’t the only threat to your security that strikes through email. Cryptolocker is just the latest.
Email security is essential for both your business or your home network. There are a number of options for enhanced email security, but regardless of what you choose, make sure it includes some vital features. Your security software should scan incoming email for known threats and separate those that are potentially harmful. Email protection has to be more intelligent than ever to properly protect you. Spammers are constantly updating their tactics to get around spam filters.
Geek Rescue offers a number of options to keep you safe from the latest cyber threats. Call us at 918-369-4335 to find out how we can protect you.
November 19th, 2013

Do you have Silverlight installed on your computer? The Microsoft product, similar to Adobe Flash, is used for running internet applications, most notably the streaming video client on Netflix. Subscribers alone account for 40-million Silverlight users worldwide. As Zeljka Zorz of HelpNet Security reports, all of these users are at risk of becoming a victim of a malware attack that exploits a critical vulnerability in Silverlight.
The malware, which could allow remote code execution, finds it way onto your machine when you visit an infected website. This website could be specifically set-up by hackers to infect unsuspecting users, it could be a compromised site that’s infecting users without the owners knowledge, or a site that allows user submitted content.
When you land on one of these websites, an Angler exploit kit, which is a tool used by hackers, determines what version of Silverlight you have installed. It determines whether you are vulnerable to an attack and, if so, the malware is downloaded to your computer.
The reason the Angler is needed is because Microsoft has already released a patch that fixes the security flaw being exploited. However, a number of users fail to update and are still using out-dated versions of Silverlight. If you’re using Silverlight, be sure you update to close vulnerabilities that could otherwise lead to a malware infection. If you don’t use Silverlight, but have it installed, you can remove it completely to protect yourself from this attack.
This is another example of why it’s important to keep all applications up to date and install each patch when it’s released. Enabling automatic updates for trusted applications makes this job easier.
If you have experienced a malware attack and your computer’s performance is suffering, bring your machine to Geek Rescue or call us at 918-369-4335.
November 18th, 2013

Computers aren’t cheap and most of us see a decline in performance of our current PC before we’re ready to invest in a new one. A post at IT Manager Daily contains some suggestions for how to improve the performance of older computers to prolong their life. Whether you want to get more out of your personal laptop, or don’t have the budget for new computers at your business, these are valuable tips.
If your PC is a couple years old, you’ve probably downloaded files and applications you don’t need. You’ve probably also encountered malware, adware or spyware that is still on your hard drive. There are tools available to do a complete scan of your system and help you remove unwanted and unnecessary files. Once you also remove the files and programs you no longer want or need, be sure to run Defrag, or defragmentation. This reorganizes data stored on your hard drive to make it more efficient. Over time, fragmentation occurs when files are saved and deleted.
At this point, you should have deleted everything that isn’t vital on your machine. Take what’s left and back it up on an external hard drive or another storage device. This is to make sure nothing is lost through the rest of the process.
New hardware, like a memory upgrade, is much cheaper than an entire new computer, but will significantly improve performance. Do some research or ask a professional about which upgrades will boost your machine’s performance the most.
With everything backed up, you can start over from scratch. Re-install your operating system, or take this chance to upgrade to one with better performance. Be sure to check for updates that you may have failed to install before. These updates often solve stability issues that could be slowing down your machine.
Once you’re back up and running, be smart about what you save on your hard drive to keep it running smoothly for longer. Use cloud storage so you don’t have to save directly to your hard drive. Keep security software updated and running to keep viruses and malware from infecting your system. Regularly go through your files and delete those you no longer need.
If you need help upgrading hardware, installing a new operating system, backing up data or removing viruses and malware, bring your computer in to Geek Rescue, or call us at 918-369-4335.
November 14th, 2013

Spam email is a common problem for anyone with an an email address. Most spam messages are easy to identify, but a practice called brandjacking muddies the distinction between legitimate email and spam. Sue Walsh, of the All Spammed Up blog, reports that a recent brandjacking spam campaign involves Dropbox and attempts to steal banking and credit card information.
This scam starts when an email that appears to be from Dropbox arrives in your inbox. There are multiple variations of the same spam email, but all contain the same basic message. Some, however, are more convincing because they eliminate the typical broken English and poor spelling that marks most spam.
The message informs users that their password is too old and needs to be replaced. Users are then directed to follow the provided link and update their password. This is actually a believable ploy because Dropbox does periodically ask users to change passwords when their account hasn’t been active for an extended period of time.
The link provided doesn’t take users to a Dropbox log-in page, however. Instead, they arrive on a site made to look like it’s owned by Microsoft and told that their browser is out of date. An update is offered up for download, which is actually a Trojan that steals banking and credit card information.
The same group suspected of this scam has brandjacked UPS, Verizon and the Better Business Bureau in the past.
No matter how believable a message is, there are still ways to see through these scams. Before following the instructions of any email, check the sender’s address. In this case, the send won’t have an ‘@dropbox.com’ address, so you can assume the message isn’t legitimate. Also, if you follow a link provided that doesn’t take you where it’s supposed to, it’s another sign that you’re being scammed.
If you have any suspicion that an email you receive from a company isn’t legitimate, contact the company directly by phone.
If your computer has been infected by malware, viruses or Trojans, or you’d like to improve your device’s security before an attack happens, contact Geek Rescue by calling 918-369-4335.
November 11th, 2013

A zero-day exploit that affects Internet Explorer, Windows XP and Windows 7 users won’t be getting a patch from Microsoft any time soon. Microsoft’s Patch Tuesday for November is only a day away and, as Paul Ducklin of Naked Security reports, news is already spreading that a patch for this exploit won’t be included.
The “remote code execution vulnerability” is dubbed a zero-day because hackers were the first to discover it. Rather than security experts, or Microsoft themselves, discovering the vulnerability and patching it, cyber criminals have been able to launch attacks in the wild before any precautions could be taken.
The attacks seen so far that exploit the vulnerability use .TIFF image files that contain malware. When a user opens the seemingly innocent image file, malware infects the machine, but no warning or notice is given. This silent infection allows hackers to remain undetected while they claim access to files and control a computer remotely.
So far, most of the attacks stem from email attachments. The .TIFF is hidden in a Word document and automatically loaded when the document is opened. There are a number of other ways the exploit could be attacked, however. Inserting the infected image file directly into the body of an email could infect your system through only a preview of the message. Hackers could also set-up websites specifically to infect visitors, or insert malware into existing sites using .TIFF images.
While there’s no patch coming from Microsoft this week, there are ways to protect yourself. A Fix it tool released by Microsoft will tell your computer to stop processing .TIFF files. This is a broad stroke, but one that will ensure the vulnerability will be closed until a more permanent patch is made available.
In the meantime, some simple advice will also help improve your security. You should always be wary of unsolicited emails and their attachments. Often, all it takes is opening the email to try to verify its authenticity is all it takes to become a victim. Also, make sure you have an antivirus program in place and it’s updated. Because of the way this exploit gives a hacker access to all of the files you’re current user account is able to access, it’s useful to use a non-administrator account. That way, if you are attacked, only part of your system is at risk, and solving the problem from an administrator account is much easier.
If any of your devices are infected with malware, bring them to Geek Rescue or call us at 918-369-4335. We’ll find the problem, fix it and help you protect yourself from future attacks.